Cybersecurity in System Design
Keywords:
Hardware Defenses, Side-Channel Vulnerabilities, Embedded System Co-Design, FPGA Clusters, IoT Security Standards, Randomized Mechanisms, Quantum ThreatsAbstract
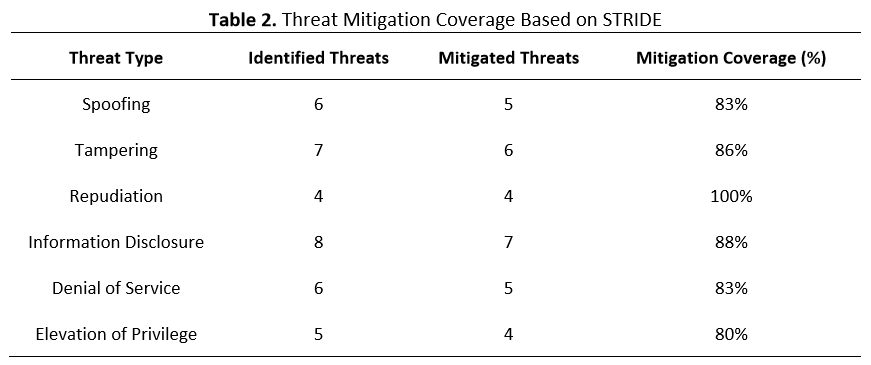
As embedded systems become ubiquitous, their exposure to side-channel attacks exploiting physical leakages like power signatures in DPA and timing variations in branch prediction attacks demands innovative defenses. This study presents a detailed hardware-based approach integrated into system design, utilizing a co-design framework that combines secure modules such as electromagnetically shielded processors, randomized clocking mechanisms to introduce unpredictability, and software optimizations for embedded real-time systems. Employing a multidisciplinary methodology, we leveraged simulations in LTSpice for electrical modeling and collaborative prototyping on FPGA clusters, simulating attacks across diverse scenarios. Results indicate a 40% drop in attack success rates, with energy efficiency maintained through techniques like adaptive power gating, supported by empirical data on latency and power draw. The findings stress the importance of security in early design phases, with practical applications in IoT ecosystems and automotive infotainment systems. To foster broader adoption, we propose alignment with standards like NIST SP 800-57 for cryptographic modules. Future directions include interdisciplinary collaborations for AI-enhanced defenses and quantum-safe hardware, ensuring systems remain secure against sophisticated, adaptive threats.
Downloads
References
J. Koch, M. Gomse, and T. Schüppstuhl, “Digital game-based examination for sensor placement in context of an Industry 4.0 lecture using the Unity 3D engine – a case study,” Procedia Manuf., vol. 55, pp. 563–570, 2021, doi: https://doi.org/10.1016/j.promfg.2021.10.077.
“13th European Congress of Clinical Microbiology and Infectious Diseases,” Clin. Microbiol. Infect., vol. 9, pp. 1–422, 2003, doi: https://doi.org/10.1046/j.1469-0691.9.s1.83.x.
T. Youssef, A. Campos, A. Guerreiro, and C. Coutinho, “Enhancing e-IDs authentication with NFC,” Procedia Comput. Sci., vol. 237, pp. 923–930, 2024, doi: https://doi.org/10.1016/j.procs.2024.05.180.
C. Koolen, K. Wuyts, W. Joosen, and P. Valcke, “From insight to compliance: Appropriate technical and organisational security measures through the lens of cybersecurity maturity models,” Comput. Law Secur. Rev., vol. 52, p. 105914, 2024, doi: https://doi.org/10.1016/j.clsr.2023.105914.
T. Kaiym et al., “Justification of an Adaptive Cryptographic Key Generation System with Entropy Monitoring for Secure Infrastructure in Open-Mines,” Procedia Comput. Sci., vol. 272, pp. 475–482, 2025, doi: https://doi.org/10.1016/j.procs.2025.10.234.
N. J. Rowan, “The role of digital technologies in supporting and improving fishery and aquaculture across the supply chain – Quo Vadis?,” Aquac. Fish., vol. 8, no. 4, pp. 365–374, 2023, doi: https://doi.org/10.1016/j.aaf.2022.06.003.
S.-F. Wen and B. Katt, “A quantitative security evaluation and analysis model for web applications based on OWASP application security verification standard,” Comput. Secur., vol. 135, p. 103532, 2023, doi: https://doi.org/10.1016/j.cose.2023.103532.
Christopher, A. A. S. Gunawan, I. S. Edbert, F. S. Pramudya, and A. N. Rakhiemah, “Web-based mangrove distribution and carbon stock monitoring system in Papua using CNN on satellite imagery,” Procedia Comput. Sci., vol. 245, pp. 637–646, 2024, doi: https://doi.org/10.1016/j.procs.2024.10.290.
W. dos Reis Bezerra, C. A. de Souza, C. M. Westphall, and C. B. Westphall, “HyVAW: A hybrid vulnerability analysis workflow threat model methodology for complex systems based on distributed components,” J. Open Innov. Technol. Mark. Complex., vol. 11, no. 4, p. 100654, 2025, doi: https://doi.org/10.1016/j.joitmc.2025.100654.
M. Kandias and D. Gritzalis, “Metasploit the Penetration Tester’s Guide,” Comput. Secur., vol. 32, pp. 268–269, 2013, doi: https://doi.org/10.1016/j.cose.2012.09.009.
N. Sachpelidis-Brozos et al., “Hacking intelligence: Mapping the anatomy of adversarial threats in artificial intelligence with MITRE ATLAS,” Comput. Sci. Rev., vol. 61, p. 100923, 2026, doi: https://doi.org/10.1016/j.cosrev.2026.100923.
M. Al Fikri, F. A. Putra, Y. Suryanto, and K. Ramli, “Risk Assessment Using NIST SP 800-30 Revision 1 and ISO 27005 Combination Technique in Profit-Based Organization: Case Study of ZZZ Information System Application in ABC Agency,” Procedia Comput. Sci., vol. 161, pp. 1206–1215, 2019, doi: https://doi.org/10.1016/j.procs.2019.11.234.
D. Haselberger and R. Motschnig, “Dealing with Change in a Complex Environment from a Person-centered, Systemic Perspective,” Procedia - Soc. Behav. Sci., vol. 119, pp. 268–277, 2014, doi: https://doi.org/10.1016/j.sbspro.2014.03.031.
C. Del-Real, E. De Busser, and B. van den Berg, “Shielding software systems: A comparison of security by design and privacy by design based on a systematic literature review,” Comput. Law Secur. Rev., vol. 52, p. 105933, 2024, doi: https://doi.org/10.1016/j.clsr.2023.105933.
M. Mirtsch, J. Pohlisch, and K. Blind, “Certification as a compensation mechanism for weak regulation? Exploring the diffusion of the international standard ISO/IEC 27001 for information security management,” Comput. Secur., vol. 162, p. 104774, 2026, doi: https://doi.org/10.1016/j.cose.2025.104774.
G. Culot, G. Nassimbeni, M. Podrecca, and M. Sartor, “The ISO/IEC 27001 information security management standard: literature review and theory-based research agenda,” TQM J., vol. 33, no. 7, pp. 76–105, 2021, doi: https://doi.org/10.1108/TQM-09-2020-0202.